#infosec #cybersecurity
Phishing, Two-factor authentication, Computer security, Security, Transport Layer Security, Protection
4.7 VMWare - How to Disrupt Cyber Attacks with a Layered Defense
One layer of defense won’t cut it given the evolving threat landscape. Find out how a layered approach might be your best defense mechanism on this upcoming webcast sponsored by @VMware. https://t.co/vsPO8yd0Ti #cybersecurity #infosec https://t.co/cQfXgB7wnz
OpenRegister for 4.7 VMWare - How to Disrupt Cyber Attacks with a Layered Defense
One layer of defense won’t cut it given the evolving threat landscape. Find out how a layered approach might be your best defense mechanism on this upcoming webcast sponsored by @VMware. https://t.co/vsPO8yd0Ti #cybersecurity #infosec https://t.co/cQfXgB7wnz
Open4.7 VMWare - How to Disrupt Cyber Attacks with a Layered Defense
Register for 4.7 VMWare - How to Disrupt Cyber Attacks with a Layered Defense
We are sorry, we could not find the related article
If you are curious about Cybersecurity Essentials and Threats and Attacks
Please click on:
Or signup to our newsletters
Security Inside the Perimeter with VMware
Businesses today are more likely to be breached now, than ever before. Thats because, traditionally, networks are architected to stop attacks at the front door instead of the infiltration ...
Webinar series: presented by the Cybersecurity Tech Accord and the Global Forum on Cyber Expertise (GFCE)
Introduction to cloud computing The webinar offers an introduction to cloud computing and demonstrates the impact of this digital transformation on security, productivity, and the way we ...
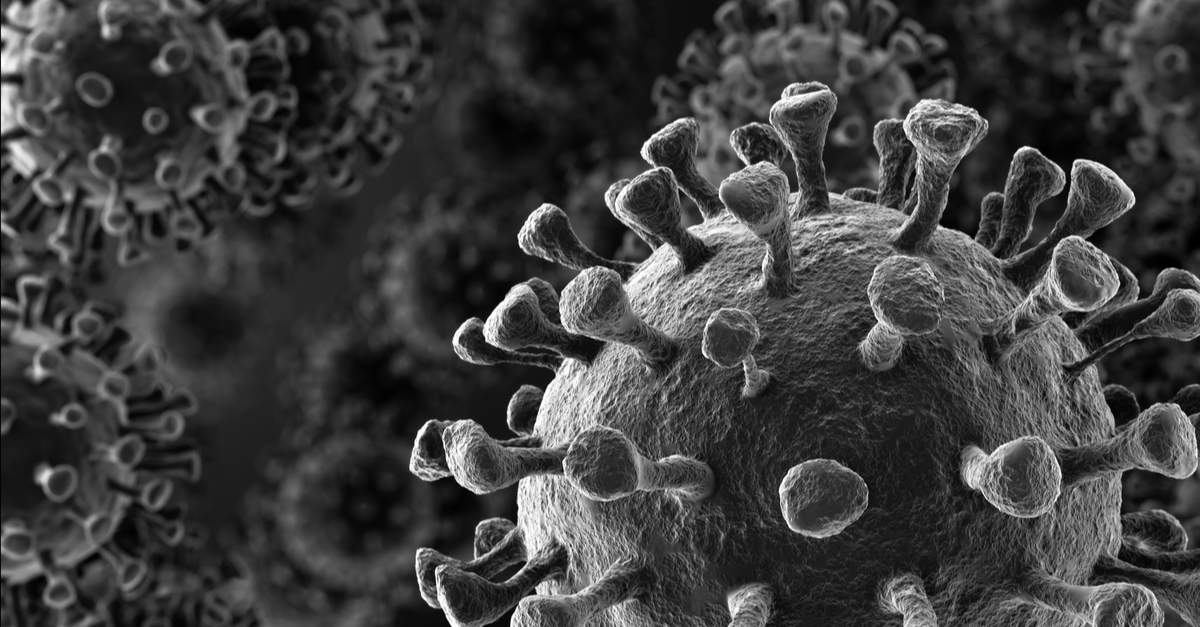
Cybersecurity guidance during the coronavirus pandemic
Best practices for secure remote working, plus the latest cyberthreats leveraging COVID-19
VMware Carbon Black Removes Endpoint Limits for Customers to Secure Their Changing Environments During the COVID-19 Crisis
Novel Coronavirus (COVID-19) has thrust personal safety and security into the public’s consciousness in an unprecedented way. Families, employees, and global businesses have been forced to ...
How to stop most cyber attacks: address human error
It’s understandable that we get frustrated when stung by a hacker, but in truth most cyber attacks can be traced back to a human error that allowed a cybercriminal to get into a system or ...
Do We Need More Cyber Hygiene?
Judging from the continued news of breaches, do we ever have enough cyber hygiene?
3 Tips to Help MSPs Prepare Clients for Ransomware Attacks
MSPs should take the opportunity to educate their clients about ransomware and other cyber threats.
Online security is an ongoing process
This is the 31st and last post in my Cyber Security Awareness Month blog series. I will do a short recap of what I covered in this series, but I also want to emphasize that online security ...
75% of European Enterprises Cite a Lack of Awareness Training a Challenge to Establish a Proper Cybersecurity Stance
75% of European Enterprises Cite a Lack of Awareness Training a Challenge to Establish a Proper Cybersecurity Stance
The Insecure Elephant in the Room
Using the web is like playing a game of Russian roulette these days — both require luck. When a dangerous link slips through security, most users must rely on their intuition when it comes ...
Cyren and Arrow Electronics Team to Deliver Cloud Security Solutions via Resellers throughout the United States and Canada
Resellers in Arrow's network will have the opportunity to sell all of Cyren's SaaS internet security products, including Cyren Email Security Gateway, Cyren Web Security Gateway, Cyren DNS ...
Cyber protection where your small or mid-sized business needs it most
Promoted | A cyberattack can cripple your business. You need the ability to assess your IT vulnerabilities and harden your system - at a price point that suits your operating expenses.
3 Tools for K-12 Cybersecurity: Keeping Schools Safe in a Digital World
Our suggestions for K-12 cybersecurity include interactive learning, best practices for configuration and resources for securing E-rate funding.