Top news of the week: 28.08.2020.
#threathunting #ShadowTalk #Cyberattacks #Data #Costs #Breach #DFIR #threatintel #infosec #PyramidOfPain
Mitre Attack
Average Cost of a Data Breach in 2020: $3.86M
When companies defend themselves against cyberattacks, time is money.
MITRE Introduces 'Shield' Defense Knowledge Base
The MITRE Corporation has taken the wraps off a knowledge base of common techniques and tactics that defenders can use to ensure their networks and assets are kept secure
RT @rickhholland: I'm thrilled to have had .@DavidJBianco join .@digitalshadows #ShadowTalk podcast. If you want to hear the origin story for the Pyramid of Pain, then this is this podcast for you. P.S. David is just a great person as well #threathunting #DFIR #threatintel https://t.co/j36p8mtrsn https://t.co/c7IieSMt3R
OpenSpecial: Guest David Bianco Talks Origin Story, Pyramid of Pain, and More
ShadowTalk hosts Alex and Digital Shadows CISO, Rick, talk to special guest David about his beginnings in the cybersecurity space, the Pyramid of Pain, and threat hunting. Pyramid of ...
Financially-Motivated Iranian Hackers Adopt Dharma Ransomware
Recent Dharma ransomware attacks show that more Iranian hackers have started to engage in financially-motivated operations
Learn about modern ransomware, extortion trends, and attacker behaviors we've learned from frontline investigations.
Register for the virtual event with our SVP and CTO of @Mandiant, Charles Carmakal, and @InfraGardNatl: https://t.co/MQL8wIiOJb https://t.co/U7fzZ2y5uj
OpenOrganizer of Ransomware and Extortion Trends Presented by Mandiant
Organizations are facing increased threats from attackers looking to make money through business disruption and extortion.
RT @emerginged1: While our first course released in partnership with @Mandiant teaches advanced technical training, we teamed up with the frontline experts once again to create a beginner-level course designed for both non-technical and technical learners: https://t.co/LNwU1pZTK8 @FireEye https://t.co/osElJgiHIA
OpenCybersecurity Awareness
Explore the foundational elements of cybersecurity programs from the experts at Mandiant, powered by EmergingEd. Enroll today.
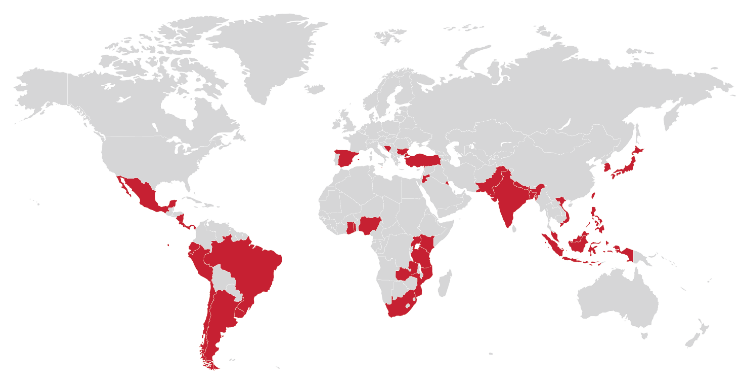
FASTCash 2.0: North Korea's BeagleBoyz Robbing Banks
This Alert uses the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK®) framework. See the ATT&CK for Enterprise framework for all referenced threat actor techniques.
RT @TrustedSec: Principal Security Consultant @rick_yocum provides a few fast and practical ways that small organizations, compliance teams, or risk management professionals can leverage the #mitreattack framework
https://t.co/D648TWYGNJ
OpenTwo Simple Ways to Start Using the MITRE ATT&CK Framework
TrustedSec's blog is an expert source of information on information security trends and best practices for strategic risk management.