Top news of the week: 23.10.2020.
#threatintel #ransomware #MITRE #cybersecurity #COVID19 #cyberrisk #riskmanagement #pandemic #cybercrime #securitytrends
Mitre Attack
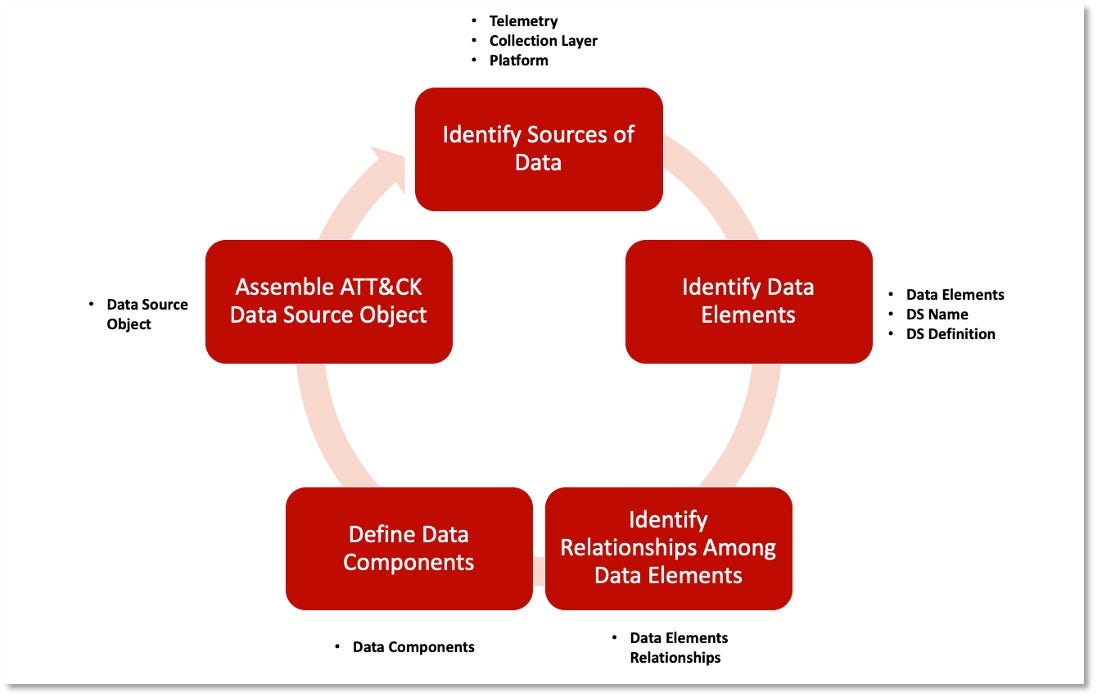
RT @MITREattack: The second part of @Cyb3rPandaH's data sources blog post, and our initial set of data source objects are now out! You can check them out at https://t.co/MVqVFY8BON and https://t.co/yeWYPpY3Kq. Let us know what you think, should this be the future of ATT&CK data sources? https://t.co/eW0DRBaSj8
OpenDefining ATT&CK Data Sources, Part II: Operationalizing the Methodology
Describing how a new data sources methodology can be implemented with ATT&CK data sources.
RT @TheDFIRReport: Ryuk in 5 Hours
➡️Zerologon (CVE-2020-1472) exploited 2 hours after initial execution of Bazar
➡️Cobalt Strike & Bazar for C2
➡️AdFind, Net, Ping, Nltest & PowerShell for Discovery
➡️WMI & RDP for Execution
➡️Ryuk ransomware for Impact
https://t.co/85P5H2eIQE https://t.co/s2fqrChs7z
OpenRyuk in 5 Hours
Intro The Ryuk threat actors went from a phishing email to domain wide ransomware in 5 hours. They escalated privileges using Zerologon (CVE-2020-1472), less than 2 hours after the initial ...
Academia Adopts Mitre ATT&CK Framework
Security pros and academic researchers discuss the best ways to use MITRE's framework to inform cybersecurity efforts, analyze threats, and teach future workers.
Are You One COVID-19 Test Away From a Cybersecurity Disaster?
One cybersecurity failure can result in a successful ransomware attack or data breach that could cause tremendous damage. There's no need to panic, but neither is there time to ignore the ...
Ransomware Attacks Show Little Sign of Slowing in 2021
Attackers have little motivation to stop when businesses are paying increasingly larger ransoms, say security experts who foresee a rise in attacks.
RT @jorgeorchilles: Tomorrow is the #WWHF #RoundUp on #adversaryemulation! We have some awesome talks planned including @MITREattack speaking on #FIN6 plan, @wh33lhouse covering how to build a program in-house, @joff_thyer covering EDR, and even some #purpleteam talks!
https://t.co/MdGaf7VTSE https://t.co/fa4ZlJ4yqY
OpenThe Roundup: Adversary Emulation
Adversary emulation is a type of ethical hacking engagement where a Red Team imitates how an attacker operates, leveraging frameworks like MITRE ATT&CK to identify specific …
RT @k_sec: "In the past year, Maze ransomware has become one of the most notorious malware families threatening businesses and large organizations. Dozens of organizations have fallen victim to this vile malware, including LG, Southwire, and the City of Pensacola" https://t.co/7NDWzZD6E0
OpenLife of Maze ransomware
In the past year, Maze ransomware has become one of the most notorious malware families threatening businesses and large organizations.
FIRST Announces Cyber-Response Ethical Guidelines https://t.co/yq1TSlepoq #infosec #incidentresponse #ITsecurity #FIRST
OpenFIRST Announces Cyber-Response Ethical Guidelines
The 12 points seek to provide security professionals with advice on ethical behavior during incident response.