Top news of the week: 19.08.2021.
Mitre Attack
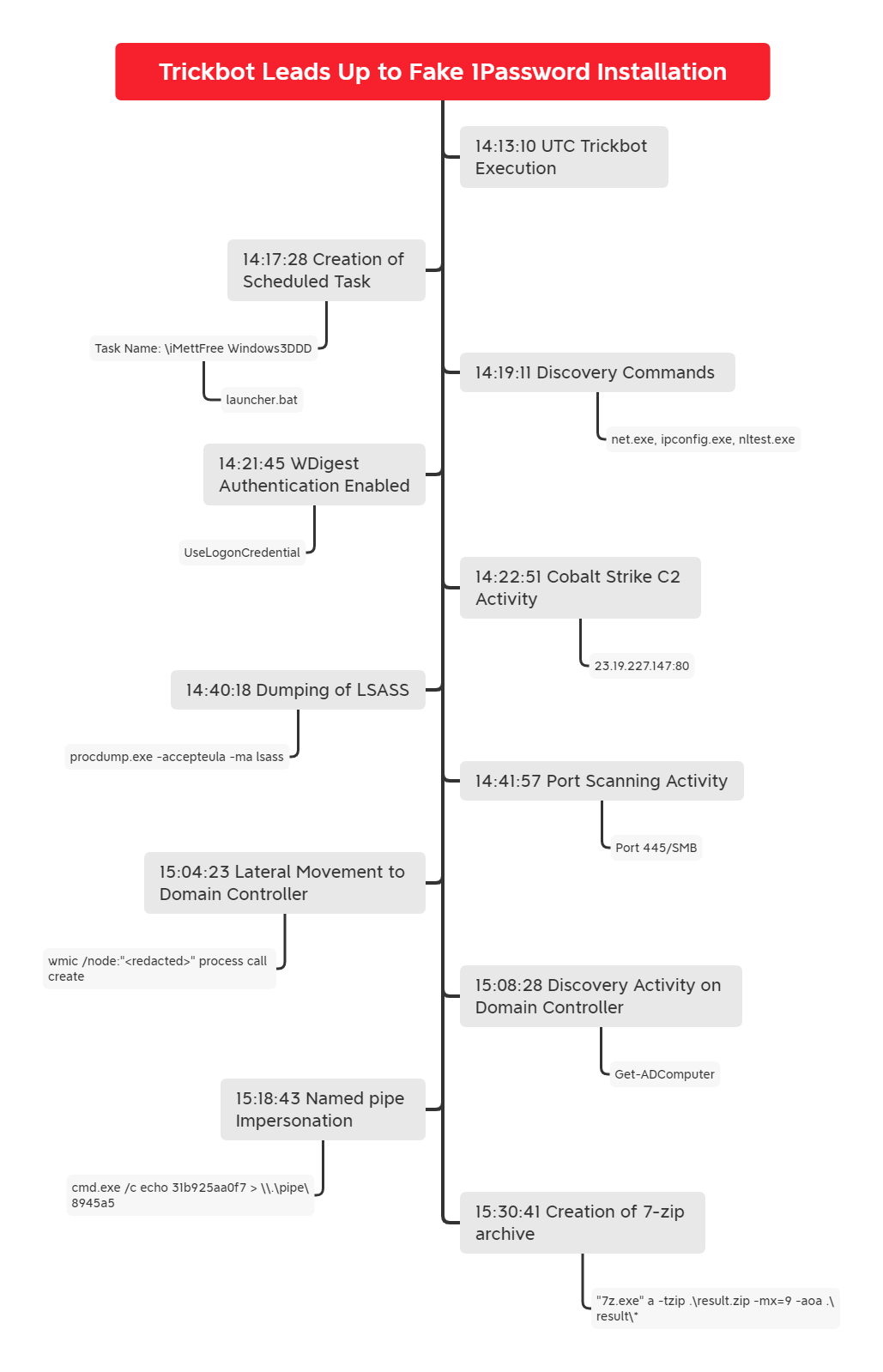
Trickbot Leads Up to Fake 1Password Installation
In this intrusion, we will take a look at a Trickbot infection, where soon after gaining access, the threat actor started to enumerate the target network and dump credential information. ...
Understanding and Improving the Burden on Threat Hunters
Report provides extensive insight into the existing role of corporate threat hunting – showing where threat hunters feel they are failing, and providing pointers on how their value can be ...
Data sovereignty laws place new burdens on CISOs
More than 100 countries now require data on their citizens be stored or processed within their boundaries, presenting new data protection challenges.
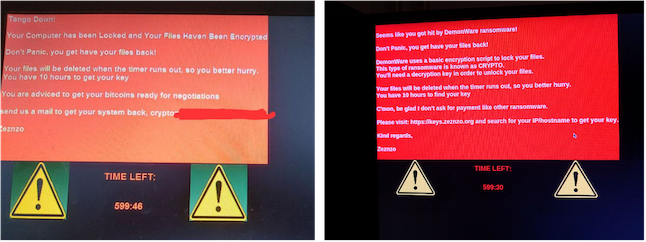
Ransomware Attacker Offers Employees a Cut if They Install DemonWare on Their Organization's Systems
Researchers went undercover and posed as willing "insider threats" to expose and study an unusual hybrid BEC-style social engineering-ransomware scheme.
How to Make Your Next Third-Party Risk Conversation Less Awkward
The SolarWinds attack has changed what companies expect from third-party vendors in order to earn their trust. That's a good thing. Here are three steps you can
Security Industry
Changing The Medical Security Industry Building the future of medical security through passion and a desire to keep people healthy. We bring together the best security experts and challenge ...
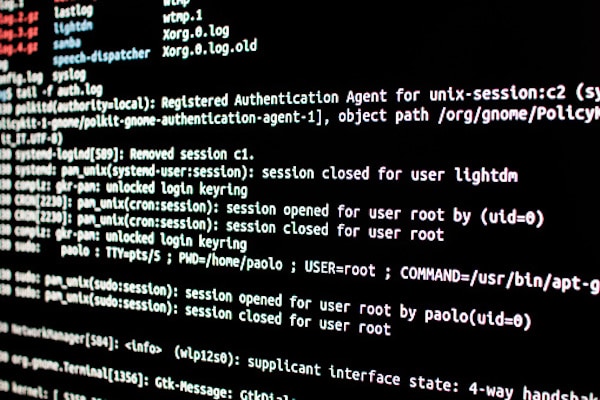
Biden Administration Executive Order Reinforces Log Standardization is Key to Security
The standardization of information system logs across the federal government may take time, but it is a critical component to improving investigative and remediation capabilities.
Analyst Report: How to Prepare for Ransomware Attacks
Security and risk management leaders need to look beyond the endpoints to help protect the organization from ransomware - fine-tuning incident response processes is a key component for ...