Top news of the week: 11.05.2021.
Mitre Attack
Why companies need a Chief Product Security Officer
RSA plans an all-virtual show starting on May 17. Today's columnist, Kacy Zurkus of the RSA Conference, writes about why companies need to strongly consider a Chief Product Security Officer ...
Threat Researcher Intern (Part-Time)
Binary Defense, headquartered in Stow, Ohio, is a rapidly growing cybersecurity software and services firm with solutions that include SOC-as-a-Service, proprietary Managed Detection & ...
Want to keep track of the latest insights and news?
Better threat intelligence with automation Good threat intelligence requires relevant context on the risks facing your organization. With Mandiant Automated Defense, our XDR …
OverWatch Threat Hunters Win the Race Against Carbanak in MITRE ATT&CK Evaluation
Read this blog to explore how CrowdStrike's world-class security team deals with a sophisticated emerging eCrime threat as it happens. Learn more here!
Exchange Exploitation: Not Dead Yet
Commentary "March Madness" is a jovial nickname for the third month of the year — but in 2021, the cybersecurity industry felt the brunt of March madness for a reason other than …
Stopping Carbanak+FIN7: How Microsoft led in the MITRE Engenuity® ATT&CK® Evaluation
In MITRE Engenuity’s recent Carbanak+FIN7 ATT&CK Evaluation, Microsoft demonstrated that we can stop advanced, real-world attacks by threat actor groups with our industry-leading security ...
Google Cloud + CrowdStrike: Transforming Security With Cloud-scale Multi-level Defense
CrowdStrike is proud to announce several service integrations with Google Cloud that deliver defense-in-depth security strategies.
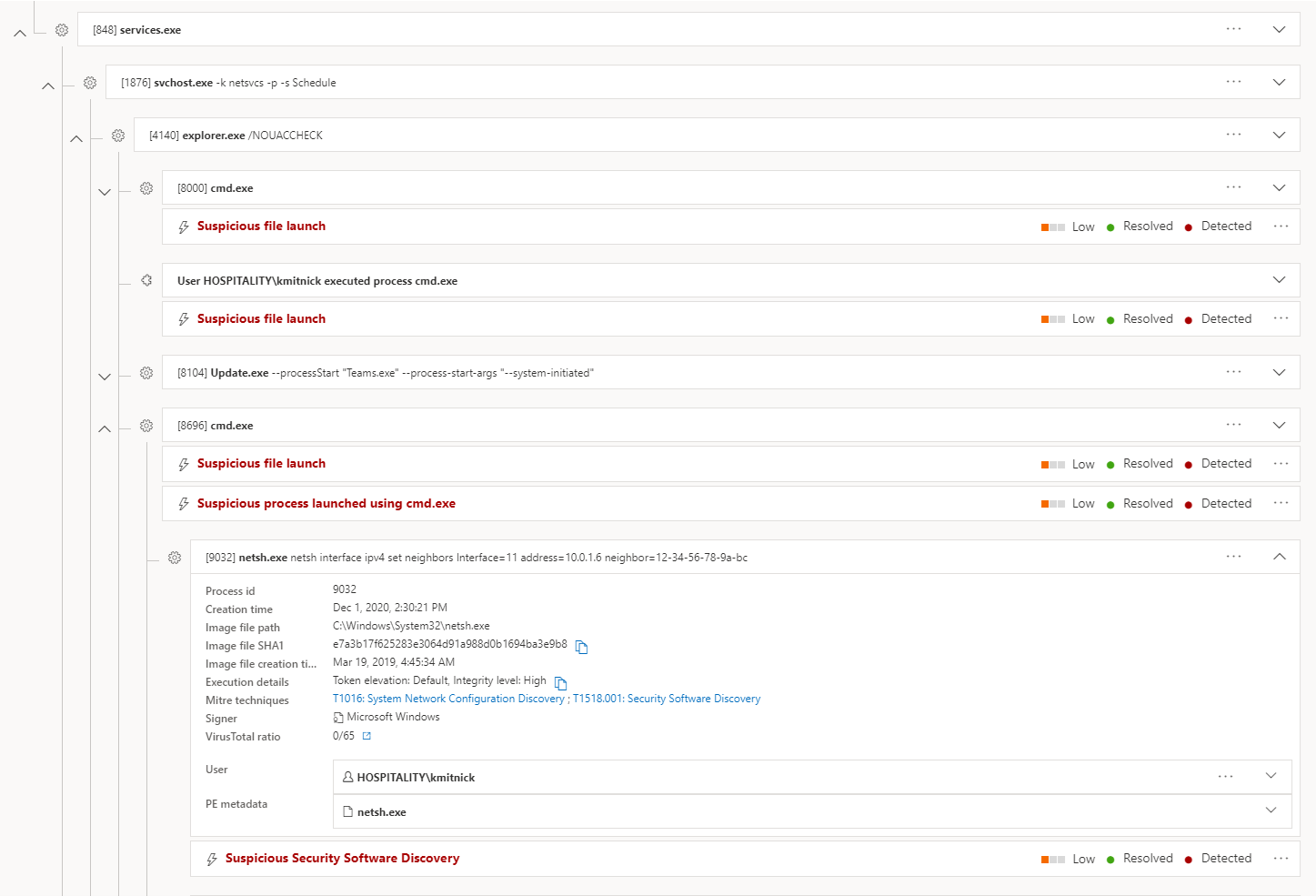
Rename System Utilities
Adversaries rename system utilities to circumvent security controls and bypass detection logic dependent on process names and process paths.