Top news of the week: 10.07.2020.
#security #AzOps #ITPRO #webinar #BlackHat2020 #infosec
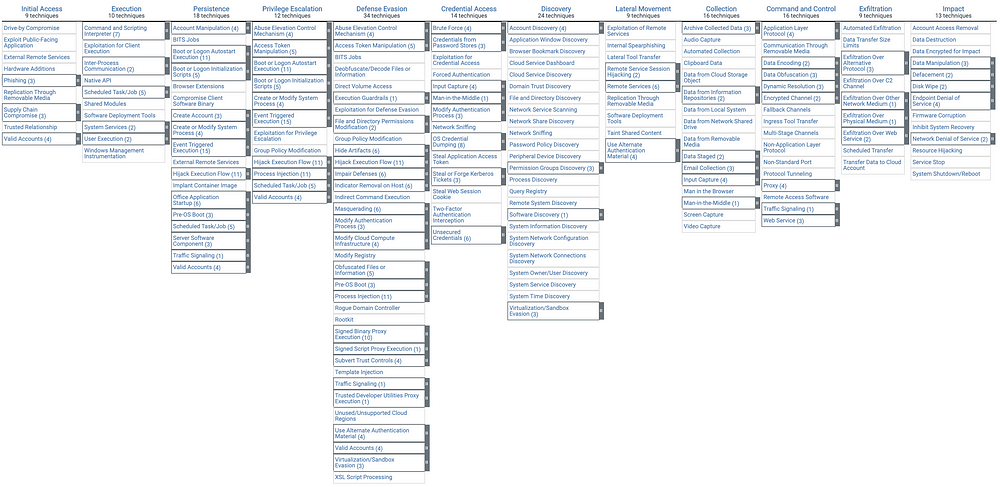
Mitre Attack
RT @MITREattack: Subs have launched! After 3 months in beta, ATT&CK with Sub-Techniques (with some small fixes) has become... ATT&CK (https://t.co/WZtpW7qSIo). We've published a new blog post (https://t.co/NEe4RrwAPY) that includes updates to our crosswalk format and describes what's changed. https://t.co/jRzl2tJu27
Open“ATT&CK with Sub-Techniques” is Now Just ATT&CK
ATT&CK with Sub-Techniques is Now Live: The what, why, and how to leverage sub-techniques.
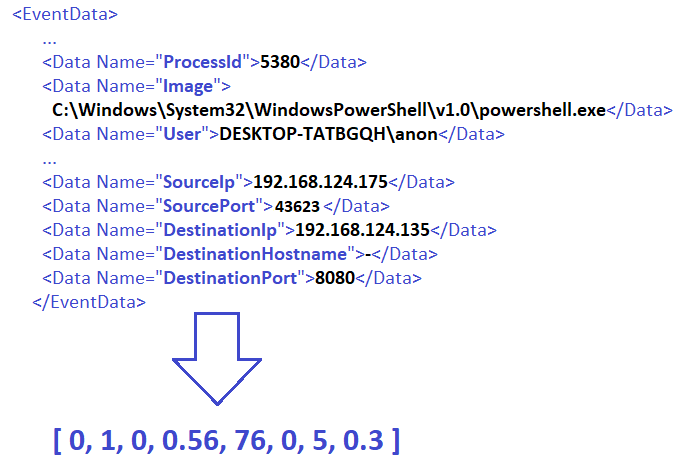
RT @ditrizna: Wonder how to apply Deep Learning for Security Detections? This research covers work with Sysmon data and RNNs: https://t.co/IFhXad8a05
Cross-references to work of @JohnLaTwC, @filar, @Cyb3rWard0g, @joshua_saxe and others. Follow them for research on advanced security analytics.
OpenSecurity Detections on Windows Events with Recurrent Neural Networks
Preprocessing of Sysmon Events, in order to use them as input of Recurrent Neural Network (RNN) model.
RT @bohops: SharpRDPHijack: A proof-of-concept .NET/C# Remote Desktop Protocol (RDP) session hijack utility
https://t.co/ueS2emOfcE
OpenSharpRDPHijack
A POC Remote Desktop (RDP) session hijack utility for disconnected sessions - bohops/SharpRDPHijack
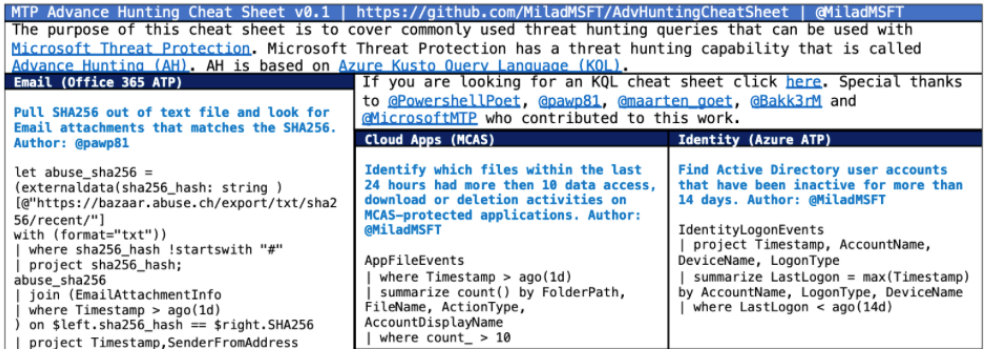
Check out our advanced threat hunting cheat sheet with best practices, shortcuts, and more, created in partnership with @Bakk3rM, @maarten_goet, @Pawp81, @PowershellPoet, @Taliash1, and @MiladMSFT. https://t.co/HqXej0YD0W
OpenMicrosoft Threat Protection advanced hunting cheat sheet
Cheat sheets can be handy for penetration testers, security analysts, and for many other technical roles. They provide best practices, shortcuts, and other ideas that save defenders a lot ...
RT @TrustedSec: Want to explore how to make better use of the ATT&CK framework? Join @RockieBrockway and @rick_yocum for our newest #security #webinar taking place 7/15 at 1pm ET. Register now!
https://t.co/4WTqZdxQKi
OpenMITRE ATT&CK™ Solutions Update and Evolution: Exploring Advanced Applications of ATT&CK
Learn more about Webinar - MITRE ATT&CK™ Solutions Update and Evolution: Exploring Advanced Applications of ATT&CK from TrustedSec, the leading US security consulting team.
Get hands-on with our award-winning Falcon platform and learn firsthand from our expert threat hunting team. Our virtual Under ATT&CK event on July 16 will share new insights and perspectives on the tactics and techniques used by today’s adversaries. https://t.co/r2gTrf0NBD https://t.co/fE0WtQLHyX
OpenNorthern European Under ATT&CK: Putting Today's Cyber Threats in Focus with MITRE Framework
16th July 2020 at 3:00pm - 4:30pm BST Virtual Event - Details to be provided upon registration EDR and threat hunting provide an unprecedented level of visibility into your …
🛡Are you ready for #BlackHat2020?
Visit our virtual booth on August 5th & 6th. Meet with our technical experts, participate in our Threat Hunting On-Demand Workshop, and more: https://t.co/1bSX3SwGek https://t.co/knClXufOhr
OpenThreat Hunting On-Demand Workshop
Learn More August 5 | On-Demand Mitigating Cyber Escalation: Modernizing Cybersecurity with Intrinsic Security Join Tom Kellermann and Greg Foss from VMware Carbon Black as they …
TAU Threat Discovery: Conti Ransomware - https://t.co/Ku4gJH9yCq #infosec via @bbaskin https://t.co/HwaprdW8Me
OpenTAU Threat Discovery: Conti Ransomware | VMware Carbon Black
Conti is a new family of ransomware observed in the wild by the Carbon Black Threat Analysis Unit (TAU). Unlike most ransomware, Conti contains unique features that separate it in terms of ...