Top news of the week: 03.07.2020.
#cybersecurity #ElasticSecurity #blog #CISOs #negotiation #leadership #LeadershipSkills #infosec #IncidentResponse #DFIRSummit
Mitre Attack
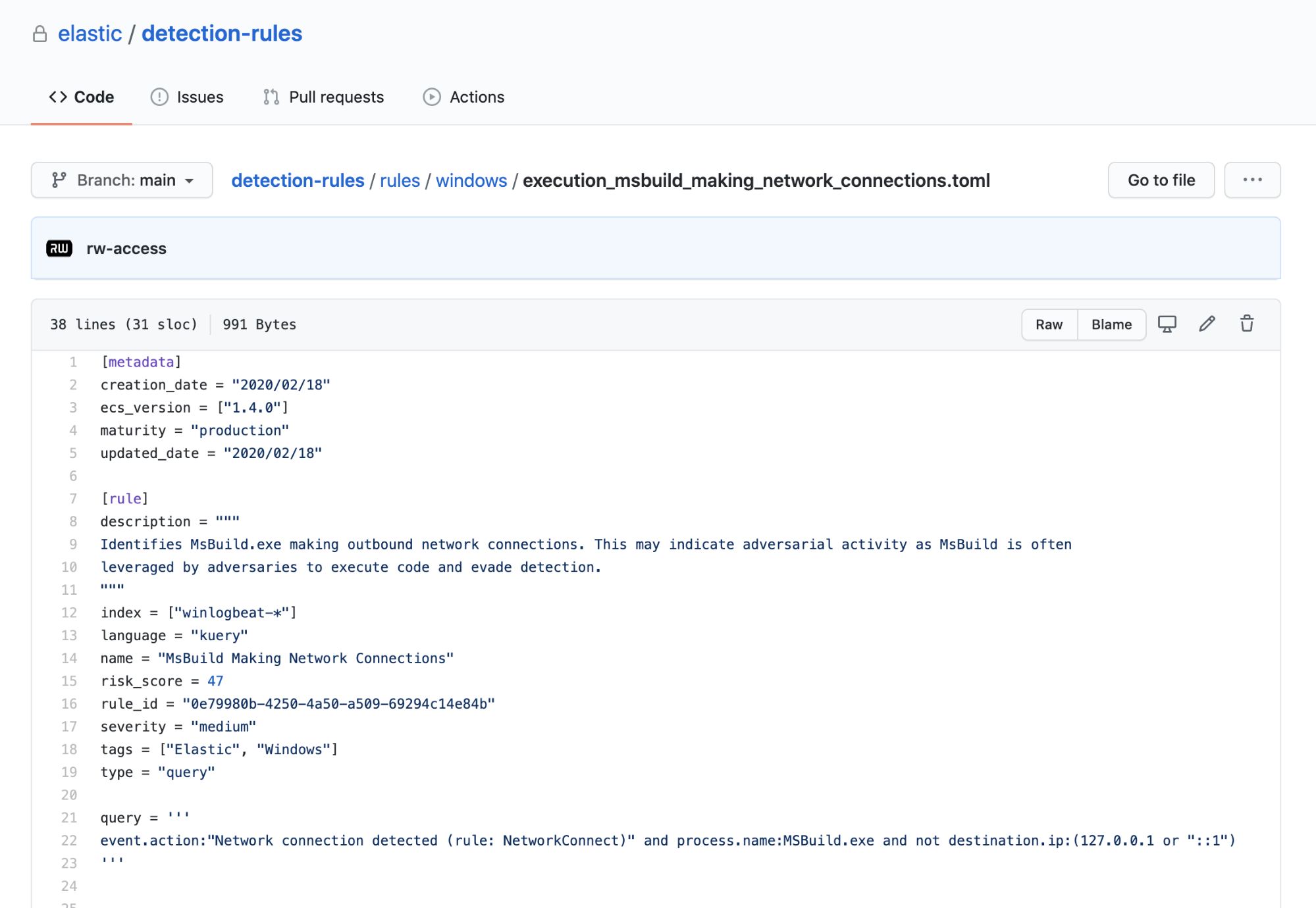
RT @elastic: In #cybersecurity, we’re stronger together. That’s why #ElasticSecurity has launched its public detection rules repo, free and open to the security community.
Read our blog post to learn how you can use and contribute to detection rules. https://t.co/RlAj9IBKgq
OpenElastic Security opens public detection rules repo
Elastic Security has opened its detection rules repository to the world. We will develop rules in the open alongside the community, and we’re welcoming your community-driven detections. ...
'GoldenSpy' Malware Uninstaller Delivered to Victims Following Public Exposure https://t.co/oJ3xpuHBW7
Open'GoldenSpy' Malware Uninstaller Delivered to Victims Following Public Exposure
Within days after a report detailing the GoldenSpy malware operation targeting organizations doing business in China, an uninstaller was pushed to affected systems to completely remove the ...
10 essential negotiation tactics CISOs should know
Lose that winner takes all mentality and build your negotiation muscle with advice from security leaders and negotiation experts.
RT @Adam_Mashinchi: The slides from my talk today:
“The Quickstart Guide to MITRE ATT&CK - Version 2.0”
Complete with speaker notes, links, and futher reading recommendations.
https://t.co/V2Z5bEDl9Q
Open[SHARED] Quickstart Guide to MITRE ATT&CK - RELOADED
Quickstart Guide to MITRE ATT&CK™ The Do's and Don’ts when using the Matrix [Version 2.0]
RT @TrustedSec: There’s a lot going on in #infosec and everyone needs a helping hand at times 🤝 Check out our latest #blog post on how we continue to build services and support to meet your needs, "Questions after an assessment? Let TrustedSec be your guide."
https://t.co/k5WqA9klhQ
OpenQuestions after an assessment? Let TrustedSec be your guide.
TrustedSec's blog is an expert source of information on information security trends and best practices for strategic risk management.
Had a great time chatting with @jorgeorchilles about emulating ransomware with @scythe_io and using Sysmon to detect it. Check out the video and blog: https://t.co/IegGkaM3Mr
Open#ThreatThursday - Ransomware
A day hardly goes by without hearing about another ransomware attack. Just this week I read, on SANS NewsBites, that University of California San Francisco (UCSF) paid $1.1 million to ...
RT @TrustedSec: When involved in an #IncidentResponse investigation, there's often confusion between expectation and reality when it comes to results. @SecShoggoth is here to clarify and set those expectations, and how to factor in Threat Hunting! #blog
https://t.co/ggErPUBpL6
OpenAre You Looking for Ants or Termites?
TrustedSec's blog is an expert source of information on information security trends and best practices for strategic risk management.
Red Canary's @PhilHagen and Frank McClain are presenting at SANS #DFIRSummit. Reserve your spot today. https://t.co/ubKTELWCQz https://t.co/dK8Kh3Opmx
OpenSANS DFIR Summit & Training | Join Red Canary live online on July 16
Register for the event and preview Red Canary's talk schedule, which include topics relevant to digital forensics and incident response professionals.