Top news of the week: 02.03.2021.
Mitre Attack
Staff Picks for Splunk Security Reading February 2021
These monthly postings will feature the favorite security-centric presentations, white papers and customer case studies from various peeps in the Splunk (or not) security world that WE ...
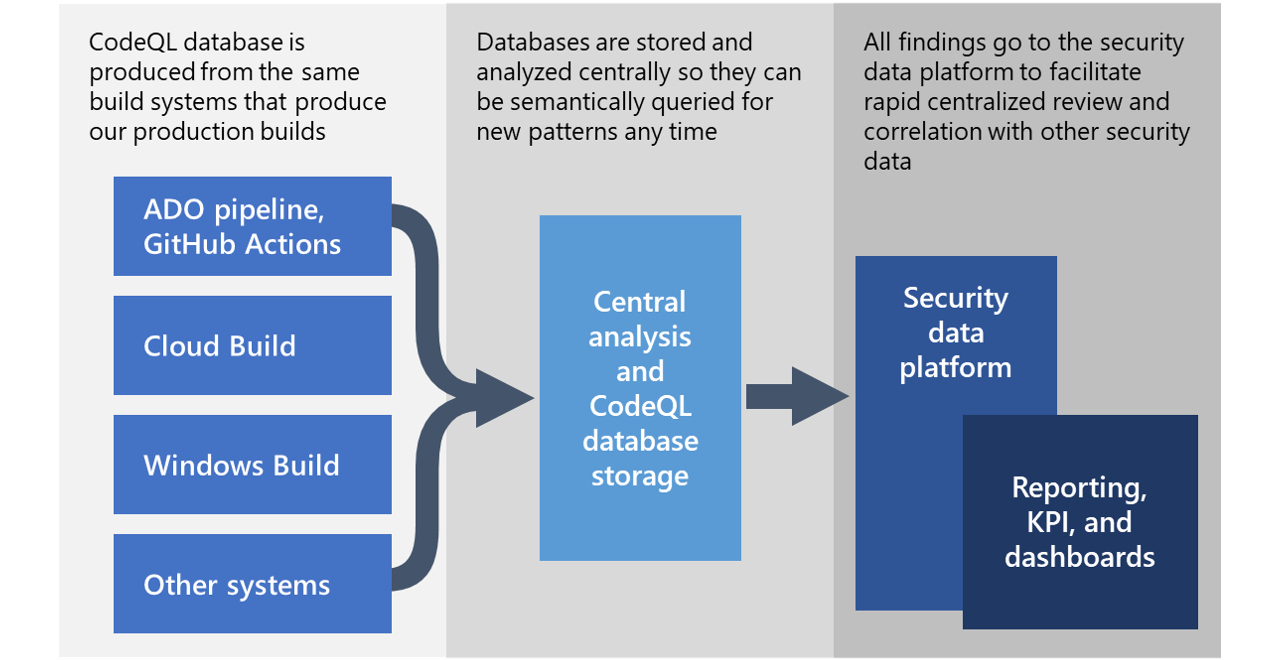
Microsoft open sources CodeQL queries used to hunt for Solorigate activity
We are sharing the CodeQL queries that we used to analyze our source code at scale and rule out the presence of the code-level indicators of compromise (IoCs) and coding patterns associated ...
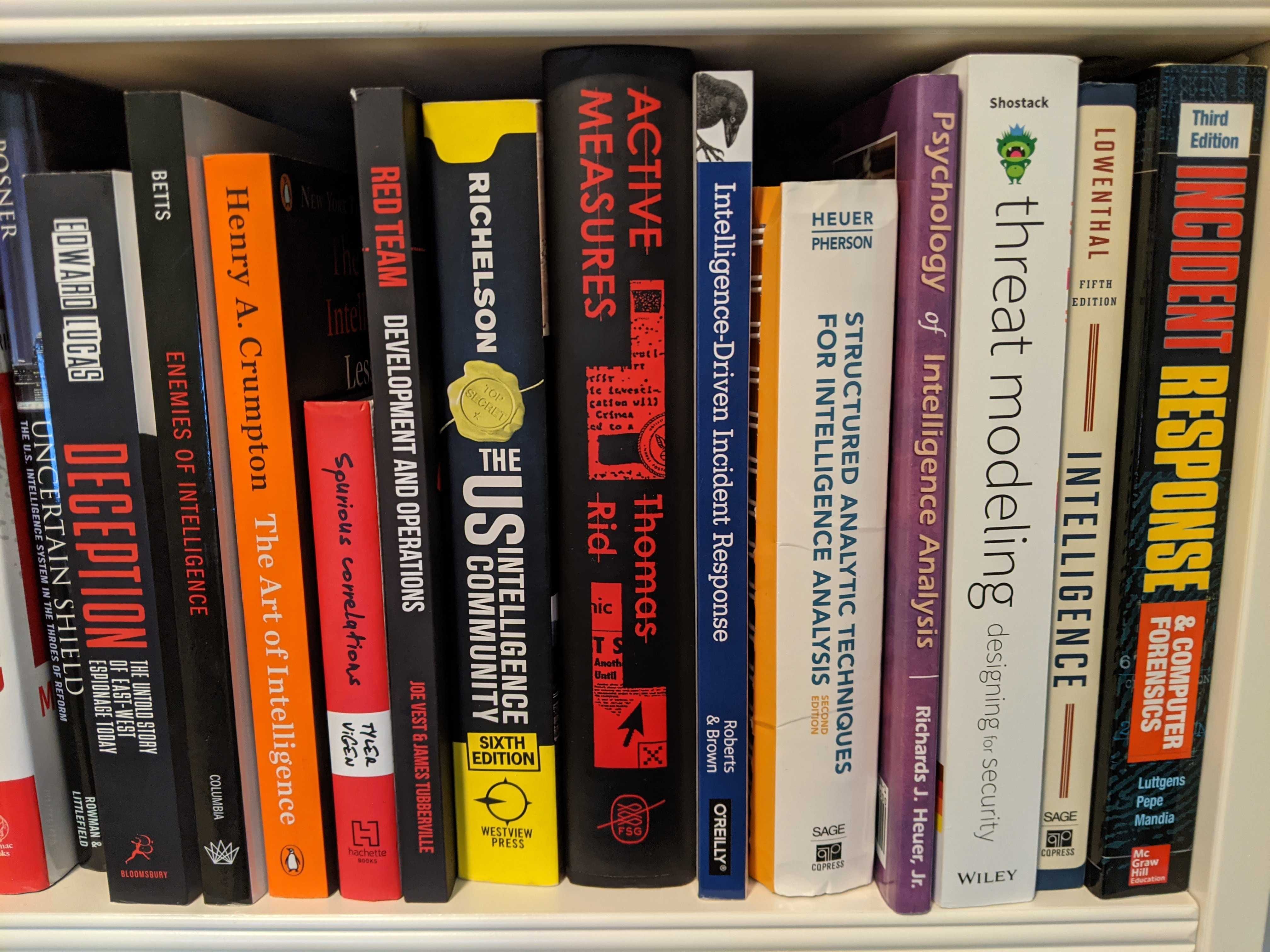
A Cyber Threat Intelligence Self-Study Plan: Part 1
There are many ways to learn. While some people prefer to have a live instructor in a course, others are great at doing self-study. I…
Hypervisor Jackpotting: CARBON SPIDER and SPRITE SPIDER Target ESXi Servers With Ransomware to Maximize Impact
By deploying ransomware on ESXi hosts, adversaries quickly increased the scope of affected systems, further pressuring victims to pay the ransom demands.
Lazarus targets defense industry with ThreatNeedle
In mid-2020, we realized that Lazarus was launching attacks on the defense industry using the ThreatNeedle cluster, an advanced malware cluster of Manuscrypt (a.k.a. NukeSped).
XDR is coming: 5 steps CISOs should take today
Beyond threat detection and response, CISOs should think of XDR as an opportunity to modernize the SOC, automating processes, and improving staff productivity. Here's your XDR game plan for ...
Security job candidate background checks: What you can and can't do
Enterprise cybersecurity begins with a trustworthy staff. Here's how to ensure that current and prospective team members aren't hiding any skeletons.
Want to keep track of the latest insights and news?
However, when SOC teams and business leaders start to lose confidence in one another, their effectiveness is likely to suffer and change will be required. This change will take …