Top news of the week: 01.12.2022.
Always Another Secret: Lifting the Haze on China-nexus Espionage in Southeast Asia
Table 2: Legitimate USB Network Gate binaries used to side-load MISTCLOAK malware The renamed USB Network Gate binaries load a MISTCLOAK DLL named u2ec.dll from the execution …
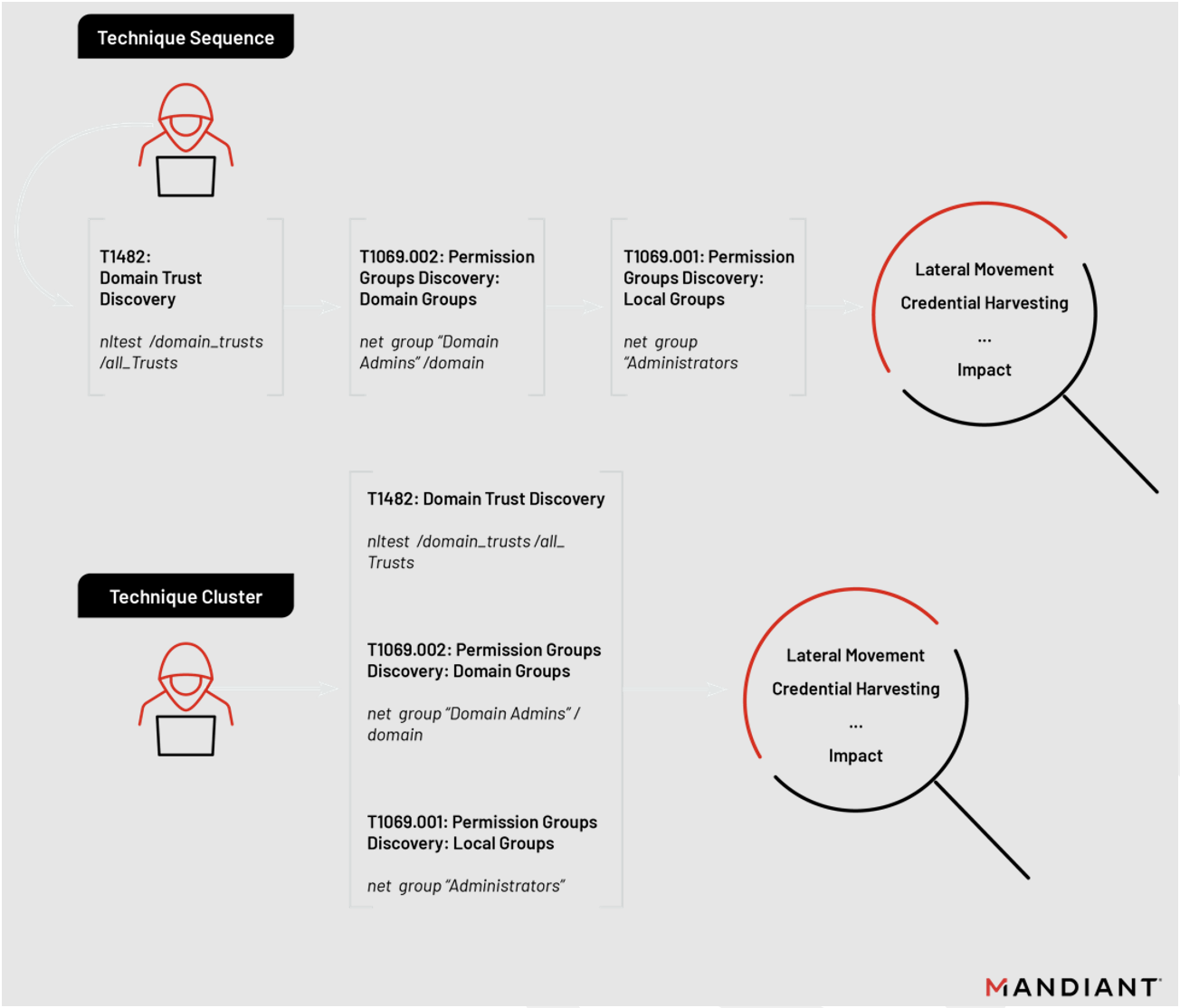
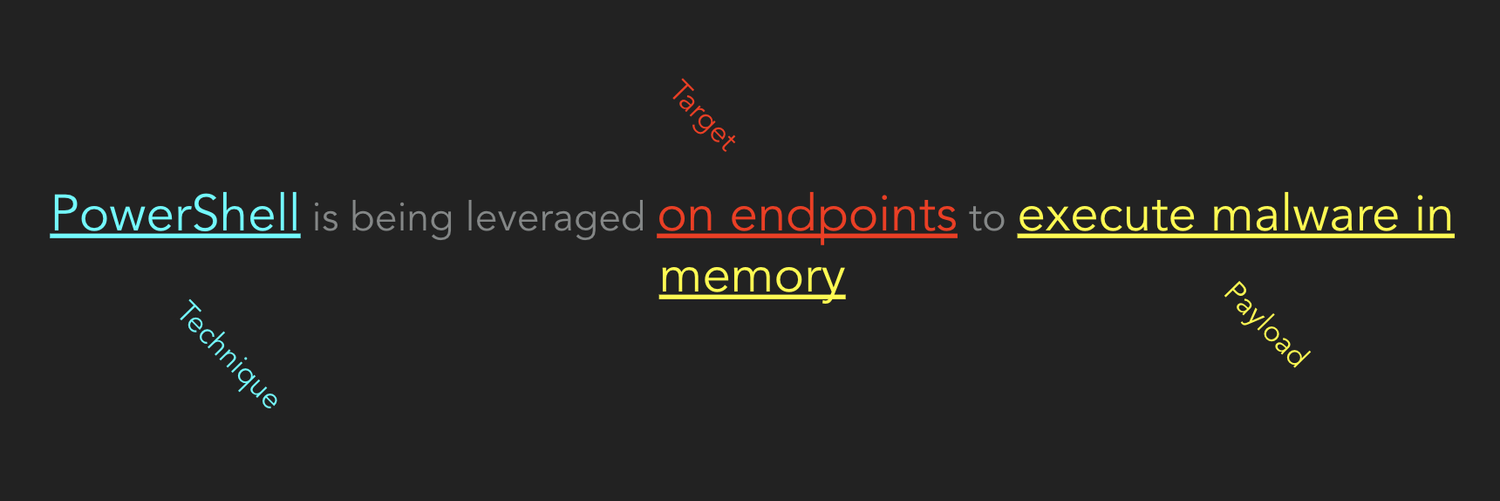
The Anatomy of a Threat Hunting Hypothesis
By now we all know that a hypothesis is a cornerstone of any threat hunt. It gives hunters their primary directive, informing every decision of discovery and analysis. Threat hunting is ...
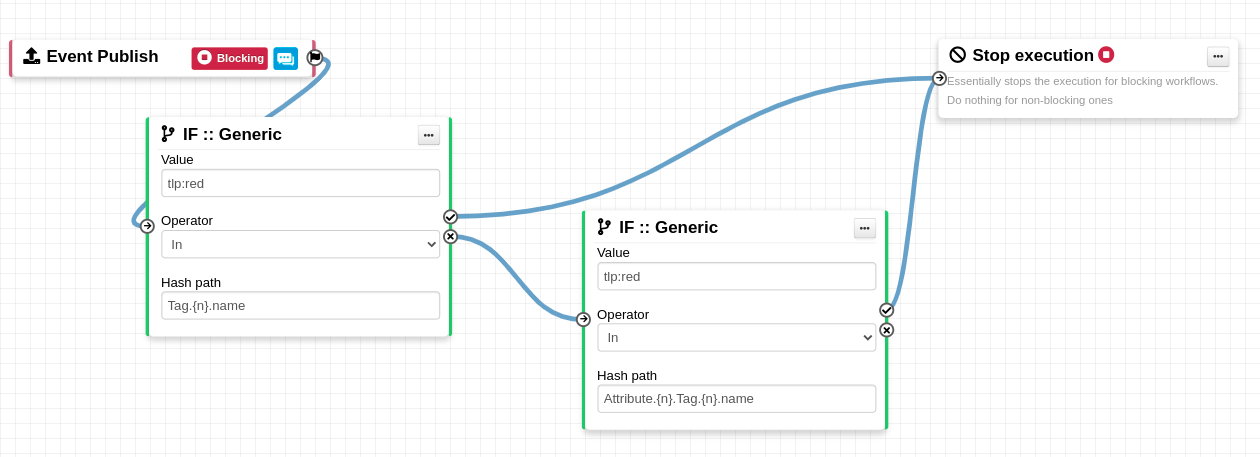
Your November Roundup: Adversaries come knocking and MITRE Evaluations are in
Your monthly roundup of Red Canary news, insights, and content is back and we've got a cornucopia of new content for you to peruse. From the MITRE ATT&CK Evaluations to Mark-of-the-web ...
The Ultimate Guide to Outsourcing Cybersecurity
How the cybersecurity-as-a-service model offers the proactive defenses necessary to mitigate cyberattacks.
Cloud Data Security 101: Learning from Attackers and Defenders
Hear from Secureworks cloud experts who address common challenges organisations face in securing their cloud environments on their digital transformation journeys.
All You Need to Know About Emotet in 2022
For 6 months, the infamous Emotet botnet has shown almost no activity, and now it's distributing malicious spam.
EU Council adopts NIS2 directive to harmonize cybersecurity across member states
The NIS2 directive replaces NIS as EU Council seeks to improve resilience and incident response capacities in the EU.