Top news of the week: 01.09.2022.
'Sliver' Emerges as Cobalt Strike Alternative for Malicious C2
Microsoft and others say they have observed nation-state actors, ransomware purveyors, and assorted cybercriminals pivoting to an open source attack-emulation tool in recent campaigns.
Webinar Thursday September 8th 2022: Ransomware Impact on Incident Response Strategies
Over the last five years ransomware operations evolved both in capabilities and the degree of organizational structure behind it. In this webinar, we’ll cover the changes, what they mean ...
Security Culture: An OT Survival Story
The relationship between information technology and operational technology will need top-down support if a holistic security culture is to truly thrive.
Cohesity Research Reveals that Reliance on Legacy Technology Is Undermining How Organizations Respond to Ransomware
Nearly half of respondents say their company relies on outdated backup and recovery infrastructure — in some cases dating back to the 1990s, before today's sophisticated cyberattacks.
Capital One Joins Open Source Security Foundation
OpenSSF welcomes Capital One as a premier member affirming its commitment to strengthening the open source software supply chain.
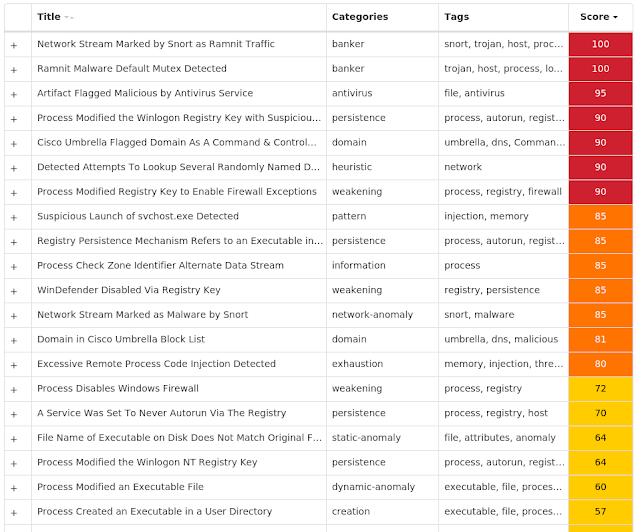
Threat Roundup for August 19 to August 26
A blog from the world class Intelligence Group, Talos, Cisco's Intelligence Group
Beyond IOCs: Validate security controls with quality threat intelligence
Leave Your IOC's at the door and learn to validate security controls with quality threat intelligence. Please join the Mandiant Behavioral Research Team as they explore the merits of ...
Key takeaways from the Open Cybersecurity Schema Format
The OCSF looks to standardize and normalize the data that cybersecurity tools generate with the goal of making them work better together.