Top news of the week: 01.05.2020.
#infosec #blueteam #incidentresponse #cyberthreat #pandemic #ITsecurity #credentials #cyberattack #databreach #ransomware
Mitre Attack
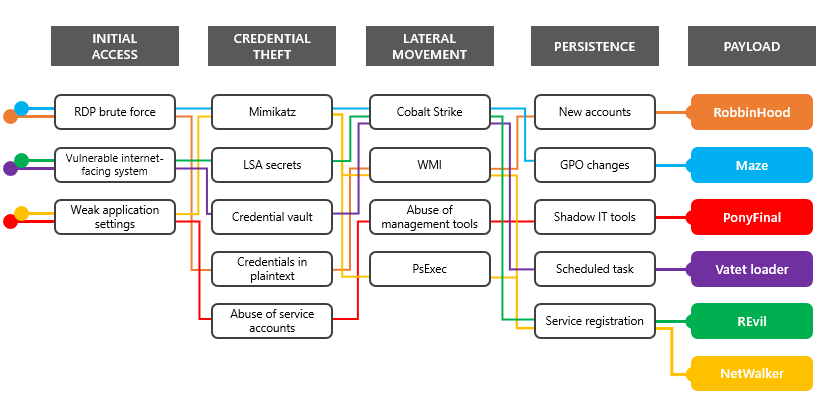
RT @MsftSecIntel: Multiple ransomware groups that have been accumulating access and maintaining persistence on target networks for several months activated dozens of ransomware deployments in the first two weeks of April. https://t.co/VwDK0v42VO
OpenRansomware groups continue to target healthcare, critical services; here’s how to reduce risk
Multiple ransomware groups that have been accumulating access and maintaining persistence on target networks for several months activated dozens of ransomware deployments in the first two ...
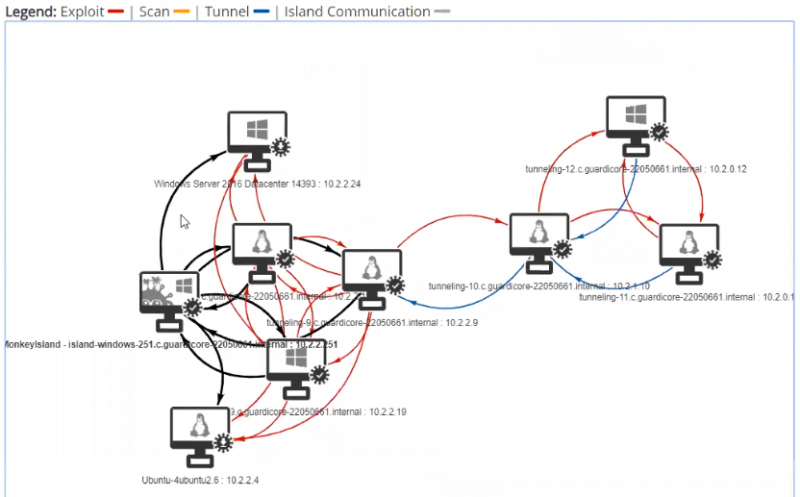
New Version of Infection Monkey Maps to MITRE ATT&CK Framework
Guardicore's open source breach and attack simulation platform Infection Monkey now maps its attack results to the MITRE ATT&CK framework, allowing users to quickly discover internal ...
Increased Credential Threats in the Age of Uncertainty
Three things your company should do to protect credentials during the coronavirus pandemic.
Top 10 Cyber Incident Response Mistakes and How to Avoid Them https://t.co/QX8ADroWtm by @ErickaChick
#cyberattack #incidentresponse #ITsecurity #databreach
OpenTop 10 Cyber Incident Response Mistakes and How to Avoid Them
From lack of planning to rushing the closure of incidents, these mistakes seriously harm IR effectiveness.
RT @SecHubb: NEW COURSE IS HERE!📣 Introducing MGT551: Building and Leading Security Operations Centers, my new 2-day class covering building, managing, testing, and improving your SOC! Info and reg. for the half-price beta July 1-2 is now live here: https://t.co/uyYbMgIRaH #infosec #blueteam https://t.co/PcuEFRKbNf
OpenMGT551: Building and Leading Security Operations Centers Beta
Computer security training, certification and free resources. We specialize in computer/network security, digital forensics, application security and IT audit.
Webcast: How to Build a Home Lab
This is a joint webcast from Black Hills Information Security and Active Countermeasures. How many of us have tried some new configuration option, utility, or hardware on a production ...
10 ways to get more from your security budget
In today's economic climate, CISOs have to make every penny count and maximize every dollar. Here’s how some do that.
RT @Cyb3rWard0g: Favorite open source libraries to connect to your favorite SIEM from a @ProjectJupyter notebook?? These are my favorite ones:
🔥 HuntLib: https://t.co/HH0K9Lb6gS (🙏 @DavidJBianco ) Connect to Splunk & ELK 💥
🔥 MSTICPy: https://t.co/T4fYzaCTMT . Connect to Azure Sentinel 🍻
Opentarget / huntlib
A Python library to help with some common threat hunting data analysis operations - target/huntlib