#partnership #infosec #cyberthreat #cyberattacks
Attack, The Weakest Link, Security, Computer security, Phishing, Weakest Link
Cybereason and TruVisor Partner to Protect ASEAN Enterprises from Advanced Cyber Threats
Cybereason and TruVisor today announced a partnership that will protect ASEAN region organizations from sophisticated cyberattacks. As part of the partnership, TruVisor will expand Cybereason’s reach with the region’s top resellers and MSSPs across Southeast Asia...
Cybereason and TruVisor Partner to Protect ASEAN Enterprises from Advanced Cyber Threats
Cybereason and TruVisor today announced a partnership that will protect ASEAN region organizations from sophisticated cyberattacks. As part of the partnership, TruVisor will expand ...
We are sorry, we could not find the related article
If you are curious about Cybersecurity and Mitre ATT&CK
Please click on:
Subscribe to Cybersecurity - Mitre ATT&CK
Navigating Insider and Outsider Threats in the Cloud
Remote working has led to an increase in cybersecurity risks with the sudden move to cloud-based infrastructures. Employees can be the weakest link in a cybersecurity defense.
Top 6 email security best practices to protect against phishing attacks and business email compromise
What should IT and security teams be looking for in an email security solution to protect all their users, from frontline workers to the C-suite? Here are 6 tips to ensure your organization ...
Energy industry vulnerable to increased cyber espionage and sabotage attacks
Interconnected systems in the energy industry increase vulnerabilities, and cyber attacks often go undetected for some time. “Espionage and sabotage attacks against CNI organizations have ...
Ways to prevent ransomware attacks: how to avoid becoming a victim
This article was written by an independent guest author. The reason why ransomware is more rampant today is simple: it’s lucrative for hackers. As high-profile examples of ransomware ...
The Biggest Cybersecurity Threats and How to Protect Your Business
Cybersecurity is a concern for every business, and it’s evolving every day. In this post, we take a closer look at the biggest cybersecurity threats to small and medium-sized businesses ...
How to Protect Against Ransomware
How to Protect Against Ransomware - Anti-phishing Solution and Security Awareness Training - Keepnet Labs - See how you can stop ransomware attacks
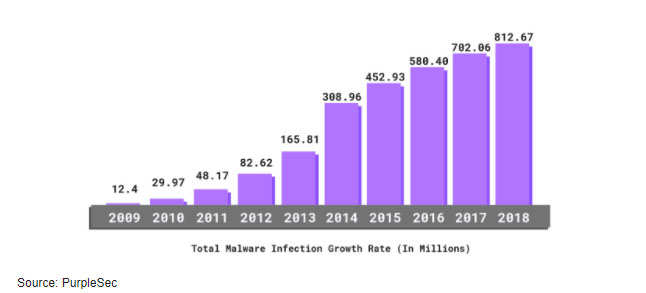
3X increase in cyber attacks results in increased budgets and attention on cyber security issues: ETILC Members
Hackers have been around for a long time and the first cyber crime occurred in the late 1970s. But over a period of time the nature of cyber attacks h..
Ransomware: the cyberthreat that just won’t die
It may have been around for 30 years, but ransomware continues to evolve and bring organizations to their knees. Make sure you’re ready for it.
NOBELIUM Demonstrates Why Microsoft Is the Weakest Link
Troubling takeaways: Microsoft essentially took a product security advisory and framed it as threat research, and less than a year after the SolarWinds attacks, Microsoft allowed the same ...
To Protect Your Company, Think Like A Thief
Put yourself in the hacker’s shoes
Insights from Experts: Kaspersky’s Lehan van den Heever on cybersecurity and artificial intelligence
Kaspersky's enterprise cybersecurity advisor, Lehan van den Heever, offers insight into how cybersecurity along with artificial intelligence is becoming critical to small, medium and large ...
The persistent humanity in AI and cybersecurity
Even as AI technology transforms some aspects of cybersecurity, the intersection of the two remains profoundly human -- attacker, target, and defender.
Selecting a managed security service
Increasingly complex IT infrastructures, higher cloud adoption rates, and a myriad of endpoints resulting from an onslaught of connected devices and
What can we do to tackle today’s phishing epidemic?
Phishing offers a great ROI for cybercriminals, but there are some simple things you can do to protect yourself. Phil Muncaster has details in this post.
Employing Robust Cybersecurity Solutions for Maritime Transportation
Maritime companies and port authorities must use constant threat monitoring and detection systems to protect against cyberattacks and prevent disturbances.
How to Remove the Target from an Agency’s Back
Educating employees and managing patches can go a long way toward making government agencies a less appealing target.