Top news of the week: 22.11.2022.
Email Cyberattacks on Arab Countries Rise in Lead to Global Football Tournament
Email security researchers from the Trellix Advanced Research Center have found attackers to be leveraging FIFA and football-based campaigns to target organizations in Arab countries.
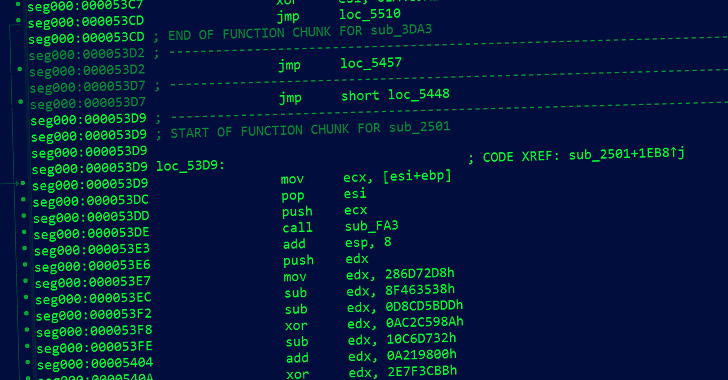
North Korean Hackers Targeting Europe and Latin America with Updated DTrack Backdoor
Hackers linked to the North Korean government have been observed using an updated version of the Dtrack backdoor to attack a wide range of industries.
Top employee cybersecurity tips for remote work and travel
During travel or when working remotely, understand your surroundings, security and risk to protect your credentials, devices and data.
Policing In The Metaverse: What’s Happening Now
The metaverse offers law enforcement agencies the opportunity to learn more about how to fight crime online, and also enables virtual training on real-world policing situations. Here’s how ...
Our Speakers
She is also a senior data protection and privacy consultant. Her experience spans compliance, corporate and ICT …
Twitter appoints 'acting DPO'
Twitter has named Renato Monteiro, FIP, acting data protection officer following the resignation of several key privacy and security personnel last week.
Rock Solid Splunk or How I Learned to Love Splunk Validated Architectures
The Splunk Validate Architectures are a professionally designed Splunk architecture intended to be deployed easily by the customer without expert assistance.
VersaBank pilots internal Digital Deposit Receipts
VersaBank has initiated an internal pilot programme of new Digital Deposit Receipts (DDRs) in Canada to validate its DDR model, CADV (for the Canadian-dollar version).
Ransomware incidents now make up majority of British government’s crisis management COBRA meetings
Ransomware incidents in the United Kingdom are now so impactful that the majority of the British government’s recent crisis management COBRA meetings have been convened in response to them ...
Researchers Quietly Cracked Zeppelin Ransomware Keys
In a blog post published today to coincide with a Black Hat Dubai talk on their discoveries, James and co-author Joel …
Are Your IoT Devices Leaving Your Network Exposed?
For years, we’ve known that Internet of Things (IoT) devices can come under attack as quickly as within five minutes of being connected to the internet. The methods hackers used to exploit ...
Zero-Trust Initiatives Stall, as Cyberattack Costs Rocket to $1M per Incident
Researchers find current data protections strategies are failing to get the job done, and IT leaders are concerned, while a lack of qualified IT security talent hampers cyber-defense ...