Top news of the week: 19.07.2022.
How to Protect Your Crypto from Hackers
Discover ways hackers steal crypto, ways to protect crypto, and an example on the importance of security best practices in blockchain exchange networks.
AI Ethics Cautiously Assessing Whether Offering AI Biases Hunting Bounties To Catch And Nab Ethically Wicked Fully Autonomous Systems Is Prudent Or Futile
The latest in AI Ethics consists of AI bias bounty hunting, though this raises a lot of questions, including as considered for aiming at AI-based self-driving cars.
Why Do Hacks Happen? Four Ubiquitous Motivations Behind Cybersecurity Attacks
At a basic level, cybercrime is typically about making money—but delving further reveals four driving forces behind cyber attacks.
Web3, ‘blockchain’ or metaverse: 7 books to understand the future of the internet
With concepts like the metaverse, the blockchainWeb3, NFTs, or the seemingly endless variety of cryptocurrencies, sometimes it feels like tech enthusiasts are trying to uproot people's idea ...
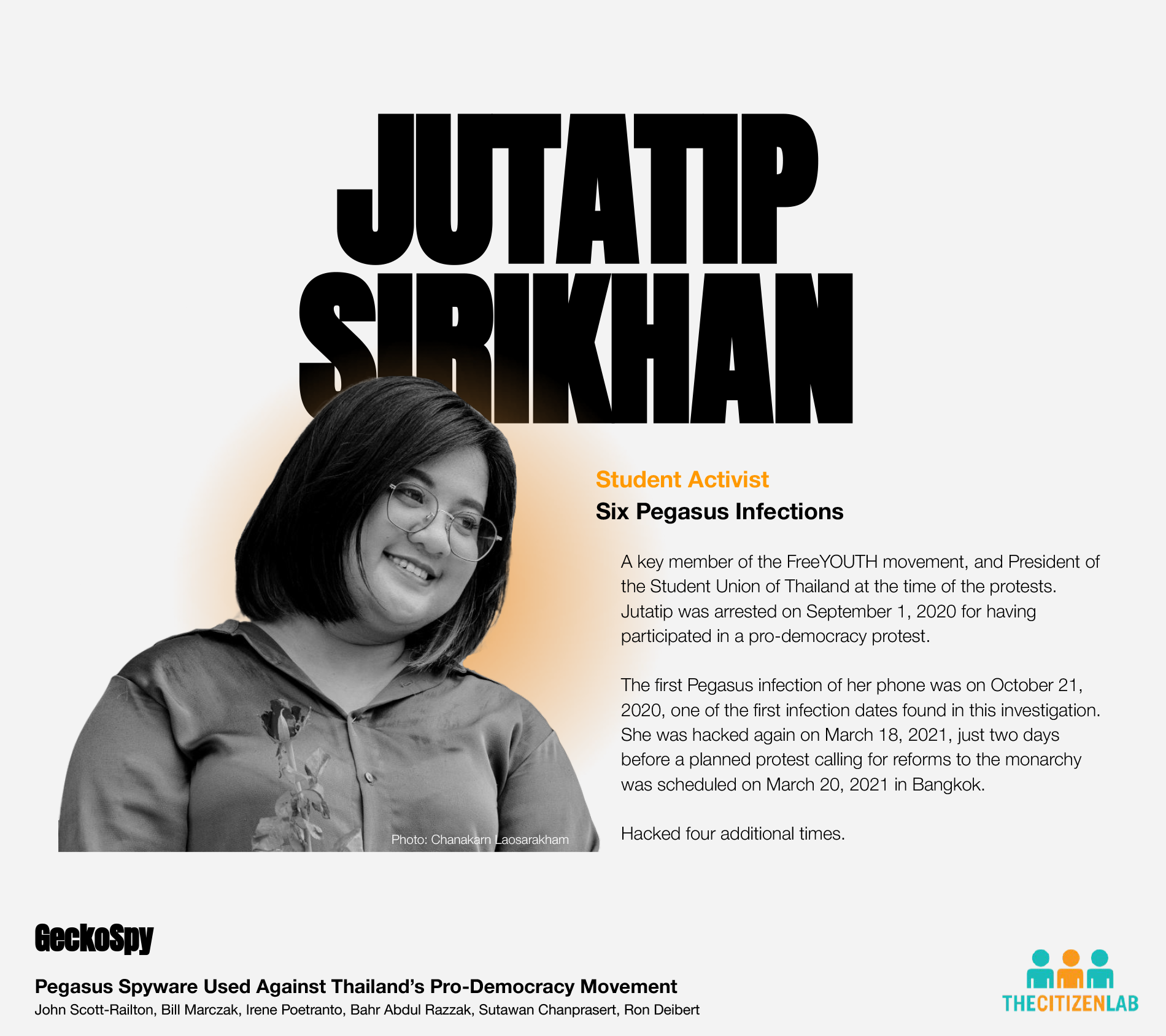
Pegasus Spyware Used Against Thailand’s Pro-Democracy Movement
Uncovering an extensive espionage operation infecting dozens of Thai pro-democracy campaigners with NSO Group's Pegasus spyware.
Homeland Security records show 'shocking' use of phone data, ACLU says
The civil liberties group released documents showing new details about how agencies had purchased information on people's movements throughout North America.
Luxembourg: Europe’s trusted data hub for internationalisation (Sponsored)
In our increasingly digital and data-driven world, there are three core pillars driving innovation that will shape the future: connectivity, cybersecurity
Thales Further Accelerates Its Cybersecurity Development With The Acquisition Of OneWelcome
Thales announces the signature of an agreement to acquire OneWelcome, a European leader for a total consideration of €100 million.
US journalists targeted by foreign hackers who show sophisticated understanding of American politics
In the days before the January 6, 2021, insurrection, Chinese hackers sent out a flurry of malicious emails to prominent White House correspondents and other journalists at major US news ...
Shining a Light on Shadow IT
Learn about the dangers of shadow IT, why users work outside the bounds of corporate IT environments, and best practices to prevent it.
DHS Review Board Deems Log4j an 'Endemic' Cyber Threat
Vulnerability will remain a "significant" threat for years to come and highlighted the need for more public and private sector support for open source software ecosystem, Cyber Safety ...
Evolution Equity TV: Who’s Who In Cybersecurity
VCs pour billions more into cyber defense startups and emerging players in 1H 2022