Risk, Vulnerability, Security, Hazard, Exploit, Computer security
Why You Should Be Using CISA's Catalog of Exploited Vulns
It's a great starting point for organizations that want to ride the wave of risk-based vulnerability management rather than drowning beneath it.
Why You Should Be Using CISA's Catalog of Exploited Vulns
It's a great starting point for organizations that want to ride the wave of risk-based vulnerability management rather than drowning beneath it.
We are sorry, we could not find the related article
If you are curious about Cybersecurity and General News
Please click on:
Subscribe to Cybersecurity - General News
Gotta Patch 'Em All? Not Necessarily, Experts Say
When it's impossible to remediate all vulnerabilities in an organization, data can indicate which bugs should be prioritized.
How Exploit Intel Makes You Less Vulnerable
Kenna and the Cyentia Institute's latest research indicates effective risk-based prioritization and risk reduction hinges on exploit intel.
CISA Adds 13 Known Exploited Vulnerabilities to Catalog
CISA has added 13 new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence that threat actors are actively exploiting the vulnerabilities listed in the table ...
HowTo: Improve Your Security Team’s Remediation Efficiency
What are the key steps to developing a risk-based vulnerability management strategy?
Vulnerability management
A well-run vulnerability management program removes the guesswork, says Katelyn Dunn. his month, we revisited a mixture of familiar and new faces.
Over 28,000 Vulnerabilities Disclosed in 2021: Report
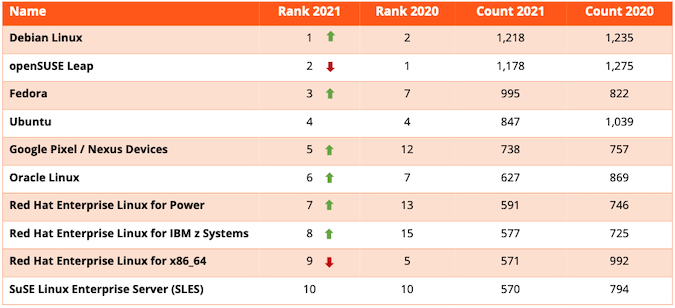
A record-breaking 28,695 vulnerabilities were disclosed in 2021, according to a report from Risk Based Security.
Vulnerability Management is Hard! Using CVSS and other scoring to prioritize patching
Vulnerability prioritization focuses on the real, urgent vulnerabilities that need to be patched at a much faster timeline than the "business as usual". This post covers various methods to ...
Davis Security Advisor extends Dynatrace Application Security with automatic vulnerability prioritization
Learn how Dynatrace has extended its Application Security with automatic vulnerability prioritization through Davis Security Advisor.
CVE + MITRE ATT&CK® to Understand Vulnerability Impact
Written by Jonathan Evans, Jon Baker, and Richard Struse.
This open-source ML model will help you predict vulnerability exploits
Most companies address the minefield of threats with no clear strategy for where to start patching and what needs prioritization.
CISA orders federal agencies to fix hundreds of exploited security flaws
CISA has issued this year's first binding operational directive (BOD) ordering federal civilian agencies to mitigate security vulnerabilities exploited in the wild within an aggressive ...
The Workforce Shortage in Cybersecurity Is a Myth
We don't have a workforce shortage problem. Application of data science to this problem has shown that companies can — and do — make meaningful risk reductions with available ...
Despite lower number of vulnerability disclosures, security teams have their work cut out for them
The number of vulnerabilities disclosed in Q1 2020 has decreased by 19.8% compared to Q1 2019, the first dip in 10 years.
NIST NVD Report Shows Increase in Low-Complexity CVEs
Vulnerabilities hit the highest spot at 18,000 till now in 2020
U.S. Federal Agencies Ordered to Patch Hundreds of Actively Exploited Flaws
CISA has ordered U.S. federal agencies to patch hundreds of actively exploited vulnerabilities.
How to Stay Cyber Aware of Weaknesses and Vulnerabilities in Your Environment
With the right approach to vulnerability management, you can identify the most pressing weaknesses in your environment and address them before attackers arrive.
Vulnerability Management: Identify, Classify, Remediate, and Mitigate
1.Vulnerability Management:
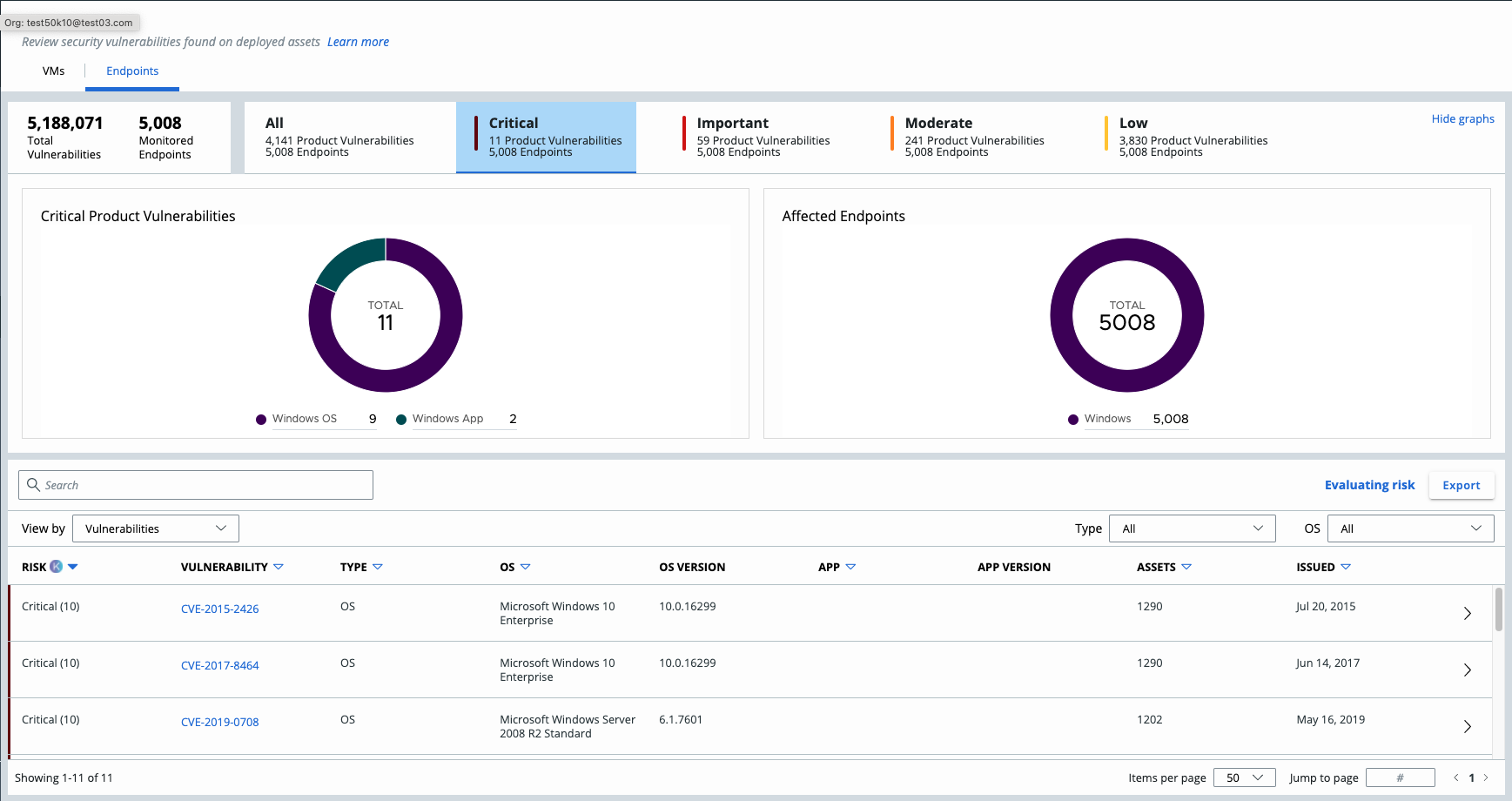
Introducing VMware Carbon Black Cloud Endpoint Vulnerability Management
Delivering risk-prioritized vulnerability management for endpoints Security and IT teams have recently been facing a tidal wave of highly publicized breaches stemming from unpatched ...