Top news of the week: 11.11.2020.
Access control, Security, Data security, United States, European Economic Community, Biometrics
Companies And Services
Trump Site Alleging AZ Election Fraud Exposes Voter Data
Slapdash setup of Trump website collecting reports of Maricopa County in-person vote irregularities exposed 163,000 voter data records to fraud, via SQL injection.
Said one expert: “It’s a mistake to think you can break encryption without breaking encryption. Once it’s broken it’s broken.” https://t.co/cYrhi9jDBQ
OpenEU resolution seeks compromise from tech firms on encryption backdoors
Some on social media speculated the resolution would be binding or that legislation was imminent. Neither are true. But it's another signal that encryption isn't settled policy in even the ...
Demand, CyberInsurance, and Automation/AI Are the Future of InfoSec
I think there are four main trends that will play out in the field of information security in the next 20 years. 1. (2021-2030) A Surge in Demand for
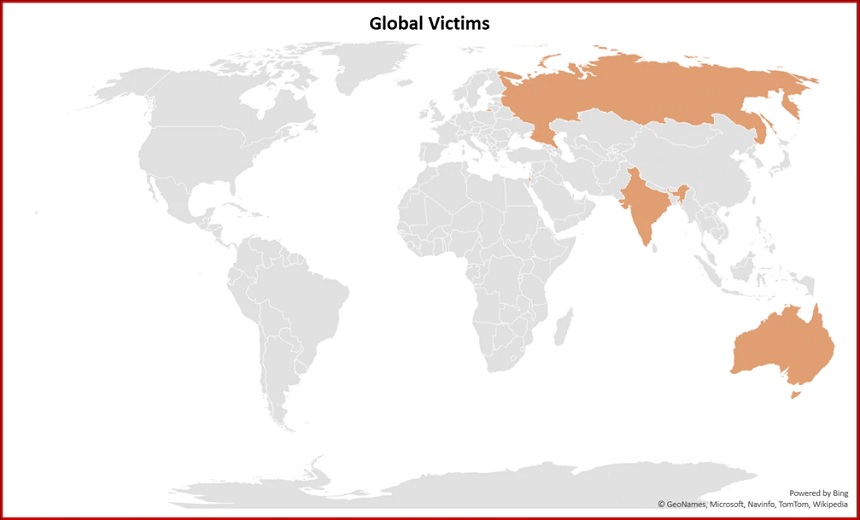
Defense Contractor Hacking More Expansive Than First Thought
A hacking operation that targeted defense contractors earlier this year was more expansive than first thought, with hackers using never-before-seen malicious tools
No cyberattack seems to have compromised the integrity of the 2020 election. Here's what to know about the steps taken to prevent and combat election interference in cyberspace: https://t.co/RheAB9ofPM via @adschina
OpenElection Security 2020
In the weeks leading up to the 2020 election, technology firms and the U.S. government took steps to prevent and combat election interference in cyberspace. Nonetheless, there were still a ...
RT @MeredithCorley: "The perimeter is now anywhere an access decision can be made" - @gattaca <--- YES.
https://t.co/ylRLN5t3Jo via @DarkReading and @kellymsheridan
OpenCloud Usage, Biometrics Surge As Remote Work Grows Permanent
A new report reveals organizations are increasing their adoption of biometric authentication and disallowing SMS as a login method.
Discover how security controls help implement a corporate security policy in our latest blog.
Read now: https://t.co/25u8JxOiTC https://t.co/Ffe11n0v49
OpenHow Do Security Controls Help Implement a Corporate Security Policy?
A corporate security policy is the cornerstone document of a company’s risk management. Does your business have the appropriate security controls in place to implement the policy, or is the ...
U.S. Tried a More Aggressive Cyberstrategy, and the Feared Attacks Never Came
The 2020 election was the biggest test yet of a new approach of pre-emptive action against adversaries trying to hack election infrastructure or wage disinformation campaigns.